Applies To: ThreatSync
As a WatchGuard Service Provider, you can create ThreatSync automation policy templates that include multiple automation policies, and then assign the template to the Subscriber accounts or account groups you manage.
Automation policy templates enable you to apply automation policies consistently across managed accounts and account groups, and save time when you set up ThreatSync for new accounts.
You can assign multiple managed accounts to the same template. However, you can assign a Subscriber account to only one automation policy template.
- If you assign an account to a second template, the new template replaces the first template.
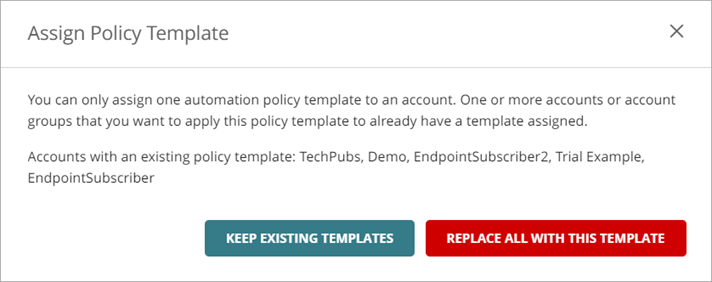
- If you assign multiple accounts to a template, and some of those accounts have an existing template assigned, you must select whether to keep or replace the existing templates for those accounts.
When you assign automation policy templates to accounts, the assigned accounts can view the policies from the templates in the Automation Policies list, but cannot edit them.
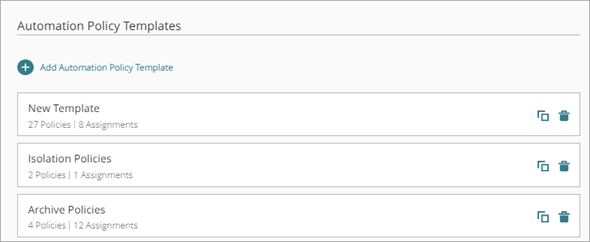
On the Automation Policy Templates page, you can:
- Add an Automation Policy Template
- Copy an Automation Policy Template
- Delete an Automation Policy Template
- View Managed Accounts with Account-Level Automation Policies
Add an Automation Policy Template
When you create an automation policy template, you assign accounts to the template and add automation policies. When you add or make changes to the policies in a template, the assigned accounts automatically receive the updated policies.
You can change the priority order of automation policies in a template to rank them from top to bottom. If an incident meets the conditions configured in multiple policies, ThreatSync performs the action specified in the highest ranked policy that applies. Each recommended action in an incident is evaluated individually against a policy. If an incident does not have a recommended action that matches an action specified in the policy, that policy is skipped. For more information, go to ThreatSync Automation Policy Precedence.
Automation policies assigned through a template appear first on the policies list in the Subscriber account.
To add an automation policy template:
-
In Account Manager, select the Service Provider account.
To select your own Service Provider account, select Overview. Or, select a tier-2 Service Provider account. -
Select Configure > ThreatSync.
The Automation Policy Templates page opens.
- Click Add Automation Policy Template.
The Add Automation Policy Template page opens.

- Enter a Name for your automation policy template.
- (Optional) Enter a Description for your automation policy template.
- In the Assignments text box, click Add Accounts.
The Add Accounts dialog box opens. - Select the account or account group you want to assign the template to.
You can only assign an account to one template. If you assign an account to a second template, the first template is removed. - If you try to assign an automation policy template to multiple accounts or account groups, and some of those accounts have an existing template assigned, the Assign Policy Template dialog box opens. Select one of these options:
- Keep Existing Templates — Assigns the new template only to selected accounts that do not have an existing template. Accounts with existing templates keep those templates.
- Replace All with This Template — Assigns the new template to all selected accounts.
- Click Add.
- Repeat steps 6 to 9 for each account you want to add.
- Add the automation policies you want to include in the template. For more information, go to Add an Automation Policy to a Template.
- Click Save.
Add an Automation Policy to a Template
When you add an automation policy, you specify the conditions and actions that ThreatSync takes on an incident. Your Service Provider account includes default automation policies with recommended settings. You can edit the default policies and configure additional ThreatSync automation policies based on the requirements of your network.
ThreatSync default automation policies are disabled by default. For new accounts, the default automation policies appear on the Automation Policies page. For existing accounts, you must click Generate Default Policies on the Automation Policies page to view them in your automation policy list. We recommend you enable the default automation policies so you can focus on incidents that require manual investigation and remediation.
For more information about ThreatSync default automation policies, go to About ThreatSync Automation Policies.
To add an automation policy to a template:
- Add or edit an automation policy template.
- Click Add Automation Policy.
The Add Policy page opens.

- To enable the new policy, click the Enabled toggle.
- Enter a Name for your policy and any comments.
- In the Policy Type section, from the Type drop-down list, select the type of policy you want to create:
- Remediation — The automation policy performs the specified remediation actions for incidents that meet the conditions.
- Close — The automation policy changes the status of incidents that meet the conditions to Closed.

- In the Conditions section, specify the conditions that an incident must meet for this automation policy to apply:
- Risk Range — Specify a range of incident risk levels. For more information, go to ThreatSync Risk Levels and Scores.
- Incident Type — Select one or more of these incident types:
- Advanced Security Policy — The execution of malicious scripts and unknown programs that use advanced infection techniques.
- Exploit — Attacks that try to inject malicious code to exploit vulnerable processes.
- Intrusion Attempt — A security event where an intruder tries to gain unauthorized access to a system.
- IOA — Indicators of Attack (IOAs) are indicators that are highly likely to be an attack.
- Malicious URL — A URL created to distribute malware, such as ransomware.
- Malicious IP — An IP address associated with malicious activity.
- Malware — Malicious software designed to damage, disrupt, and gain unauthorized access to computer systems.
- PUP — Potentially Unwanted Programs (PUPs) that might install when other software installs on a computer.
- Virus — Malicious code that enters computer systems.
- Credential Access — AuthPoint incident that indicates attempts to compromise account credentials.
- Malicious Access Point — An unauthorized wireless access point connected to your network or operating in your airspace.

- Device Type — Select one or more of these device types:
- Firebox
- Endpoint
- AuthPoint
- Access Point


-
Actions Performed — Select one or more of these actions performed on an incident (Close policy type only).
- Allowed (Audit Mode) — Incident detected, but because the device is in Audit mode, no action was taken.
- Connection Blocked — Connection blocked.
- Process Blocked — Process blocked by an endpoint device.
- Device Isolated — Communication with device is blocked.
- File Deleted — File was classified as malware and deleted.
- IP Blocked — Network connections to and from this IP address are blocked.
- Process Killed — Process ended by an endpoint device.
- Detected — Incident detected but no action was taken.
- User Blocked — Credential Access incident in which the user was blocked in AuthPoint.

- In the Actions section, from the drop-down list, select whether you want to perform or prevent specified actions.
- Perform — ThreatSync performs the specified actions for new incidents that meet the policy conditions.
- Prevent — ThreatSync prevents the specified actions. To create an exception to a broader Perform policy, you can add a policy with the Prevent action and rank it higher than the other policy in the policy list. A policy with the Prevent action does not prevent the manual execution of an action by an operator.
- Select one or more of these actions to perform or prevent:
- Block Threat Origin IP (only external IPs) — Blocks the external IP address associated with the incident. When you select this action, all Fireboxes with ThreatSync enabled in the WatchGuard Cloud account block connections to and from the IP address.
- Delete File — Deletes the flagged file associated with the incident.
- Isolate Device — Isolates the computer from the network to prevent the spread of the threat, and to block the exfiltration of confidential data. When you select Isolate Device as the action, you can specify isolation exceptions to allow communication from processes you select. For more information, go to Isolation Exceptions.
- Kill Malicious Process — Terminates a process that exhibited malicious behavior associated with the incident.
- Close the Incident — Changes the incident status to Closed(Close policy type only).
If the policy type is Close, the Close the Incident action is selected automatically and you cannot select a different action.

- Click Add.
The new policy is added to the policy list.
Isolation Exceptions
When you choose Isolate Device as the action in an automation policy, you can create exceptions to the isolation to allow communications from specific processes.
To create an isolation exception in an automation policy:
- On the Add Policy page, in the Actions section, select Isolate Device.
The Isolate Device section appears. - Enable Advanced Options.
The Advanced Options section appears.

- In the Allow Communication from these Processes text box, enter the names of the processes you want to allow as exceptions to the isolation. For example, enter chrome.exe to allow communication with Google Chrome.
- (Optional) If you want a message to show on isolated devices, enable Show Message on Device and enter a custom message in the Show Message on Device text box. If you do not want a message to show on isolated devices, disable Show Message on Device.
- Click Add
Disable an Automation Policy in a Template
On the Edit Automation Policy Template page, you can disable one or more automation policies in a template and then enable them at a later time.
To disable an automation policy in a template:
- In Account Manager, select the Service Provider account. To select your own Service Provider account, select Overview. Or, select a tier-2 Service Provider account.
-
Select Configure > ThreatSync.
The Automation Policy Templates page opens. - Select the template you want to disable the automation policy for.
The Edit Automation Policy Template page opens. - In the row for the automation policy, disable the Enabled toggle.
- Click Save.
Delete an Automation Policy from a Template
On the Edit Automation Policy Template page, you can delete an automation policy from a template.
To delete an automation policy from a template:
- In Account Manager, select the Service Provider account. To select your own Service Provider account, select Overview. Or, select a tier-2 Service Provider account.
-
Select Configure > ThreatSync.
The Automation Policy Templates page opens. - Select the template you want to delete an automation policy from.
- Next to the name of the policy you want to delete, click
 . Click Delete.
. Click Delete. - Click Delete.
- Click Save.
Copy an Automation Policy Template
On the Automation Policy Templates page, you can copy an automation template and use it as a start point for a new template.
To copy an automation policy template:
- In Account Manager, select the Service Provider account. To select your own Service Provider account, select Overview. Or, select a tier-2 Service Provider account.
-
Select Configure > ThreatSync.
The Automation Policy Templates page opens. - In the row for the template you want to copy, click
 .
.
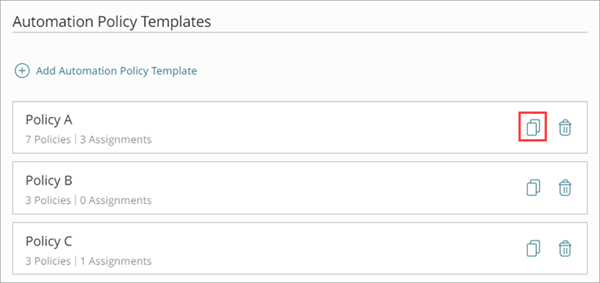
- On the Copy Automation Policies Template page, enter a Name for the new template.
- Make changes to the template, as required.
- Add assignments
- Add or delete policies
- Enable or disable policies
- Click Save.
Delete an Automation Policy Template
On the Automation Policy Templates page, you can delete an automation template if it is not assigned to any account you manage.
To delete an automation policy template:
- In Account Manager, select the Service Provider account. To select your own Service Provider account, select Overview. Or, select a tier-2 Service Provider account.
-
Select Configure > ThreatSync.
The Automation Policy Templates page opens. - In the row for the template you want to delete, click
 .
.
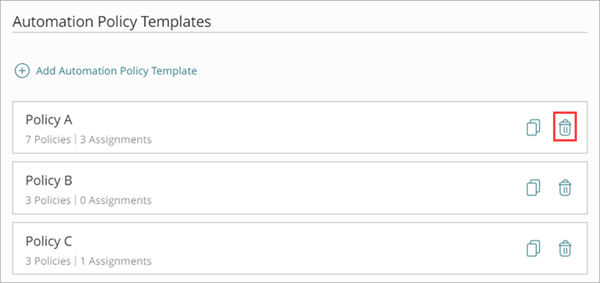
- Click Delete.
- Click Save.
View Managed Accounts with Account-Level Automation Policies
On the Automation Policy Templates page, you can view a list of your managed accounts with account-level automation policies and deploy any pending policy changes.
To deploy pending policy changes for one or more managed accounts:
- Next to the managed account with pending policy changes, click Deploy.
- To deploy pending policy changes for multiple managed accounts, click Deploy All Pending Changes.
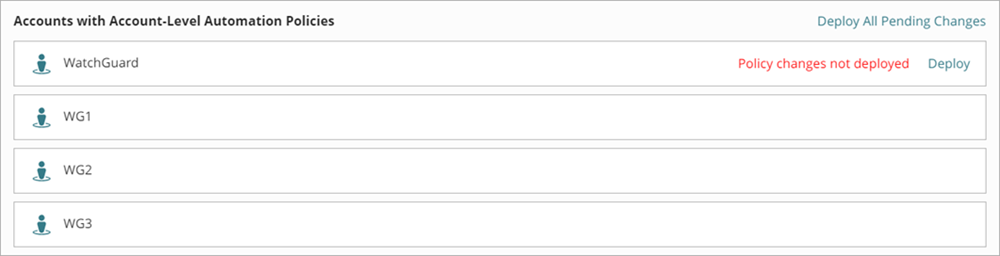
The changes deploy to the ThreatSync decision engine, which then sends actions to WatchGuard devices or services when incidents match the automation policy.
About ThreatSync Automation Policies
Manage ThreatSync Automation Policies (Subscribers)